

Why Choose Thales HSMs?
- Unmatched Security: Keys never leave the FIPS-validated, tamper-evident, and intrusion-resistant hardware.
- Hardware-Based Protection: All cryptographic operations happen inside the HSM with robust access controls to prevent unauthorized access.
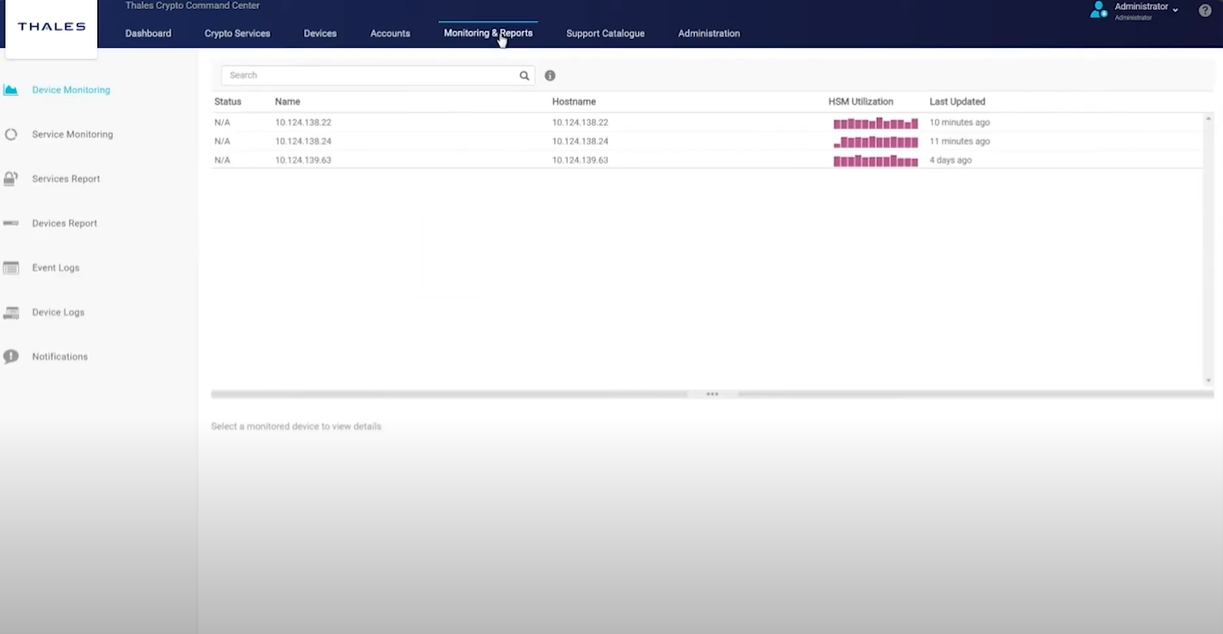
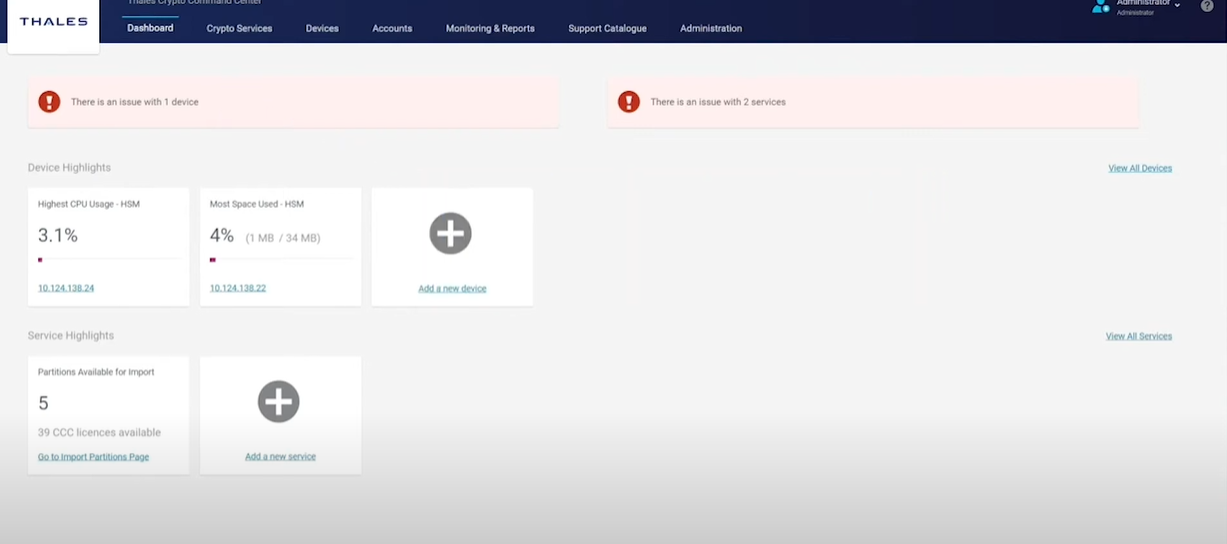
- Operational Simplicity: Integrated with Thales Crypto Command Center for intuitive provisioning, partitioning, and monitoring of crypto resources.
- Trusted Globally: Rigorously tested and validated for real-world use in the most security-conscious environments.


